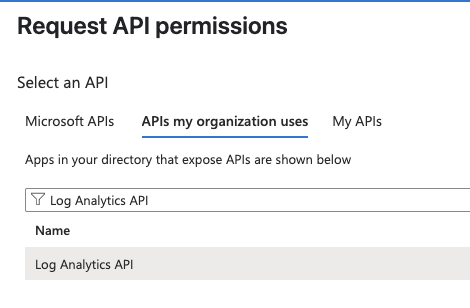
Select Log Analytics API
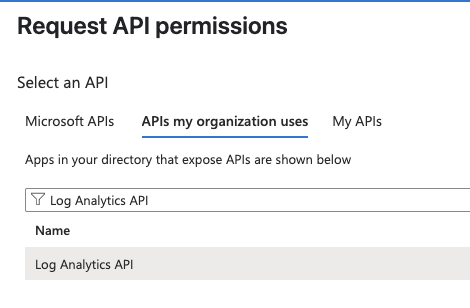
Select Log Analytics API
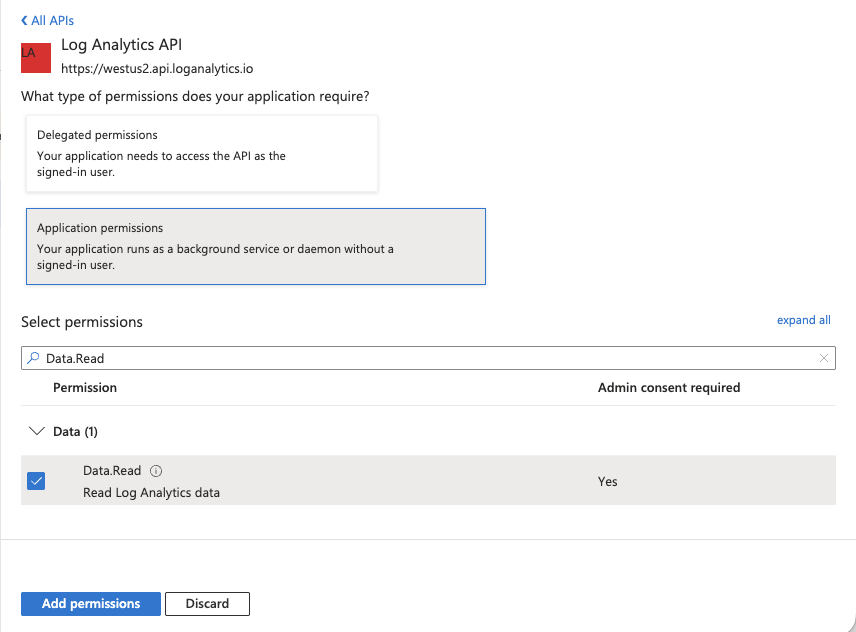
Add the Data.Read permission
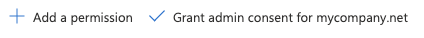
Grant admin consent
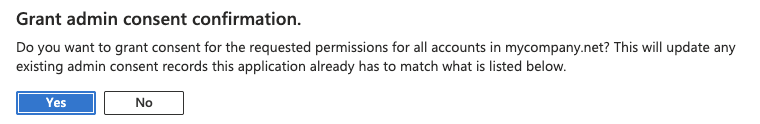
Grant admin consent
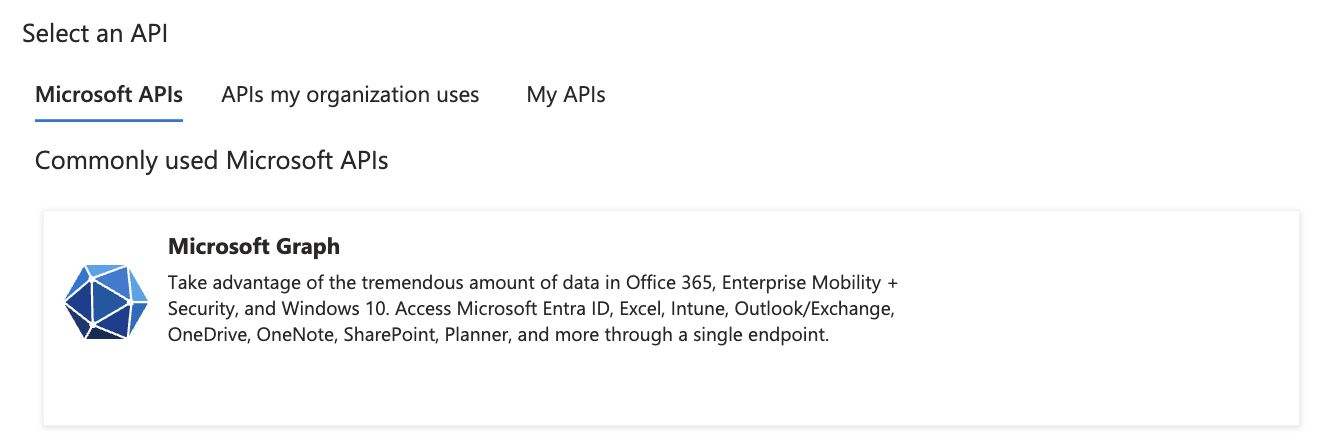
Select Microsoft Graph
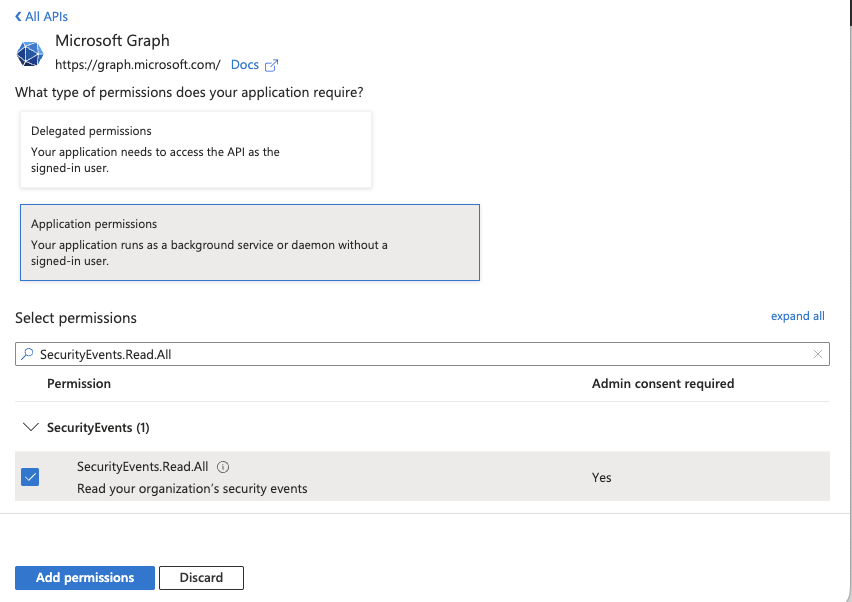
Add the SecurityEvents.Read.All permission
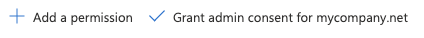
Grant admin consent
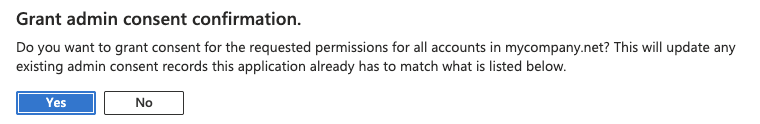
Grant admin consent
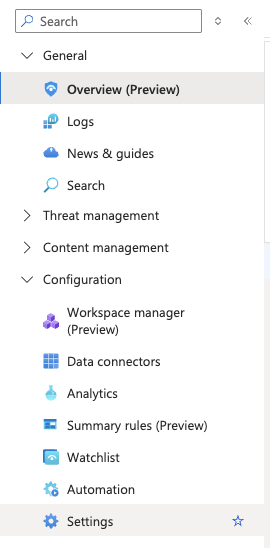
Navigate to Microsoft Sentinel
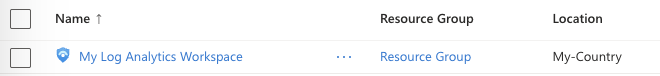
Select your workspace
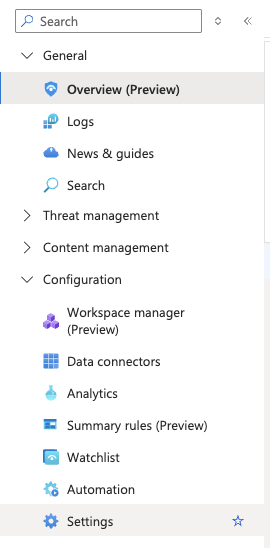
Navigate to Settings
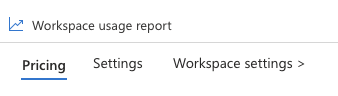
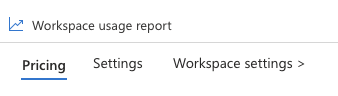
Click on Workspace settings
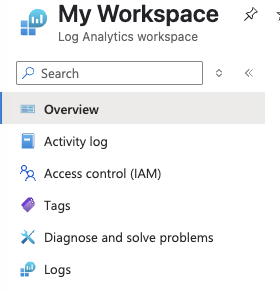
Click on Access control (IAM)
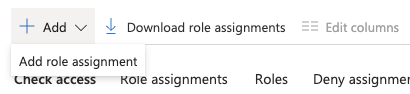
Add a role assignment
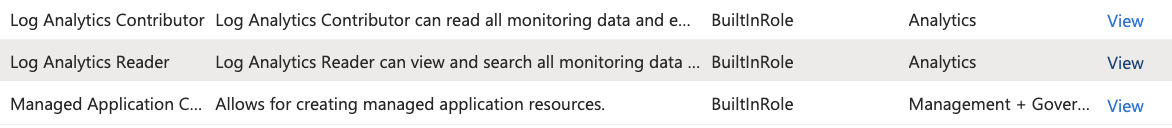
Select your role
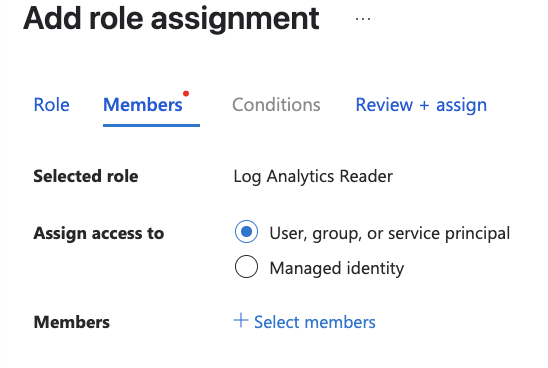
Click Select members
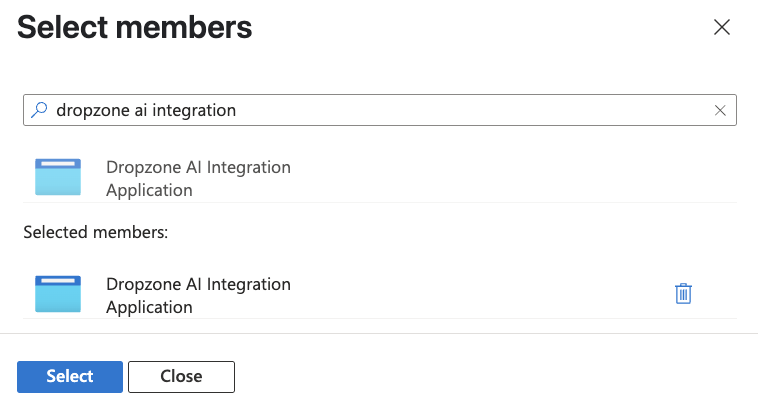
Assign members

Click Review + assign
Navigate to Microsoft Sentinel
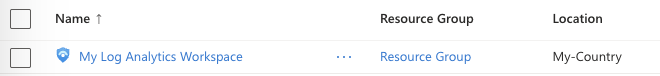
Select your workspace
Navigate to settings
Navigate to settings
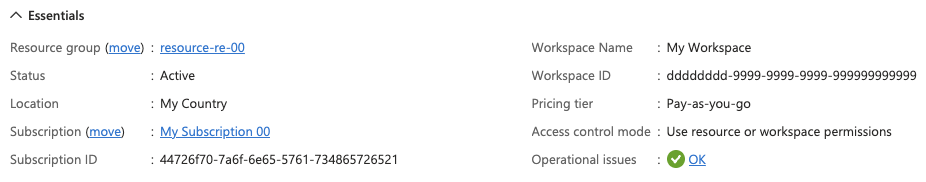
Copy the integration details
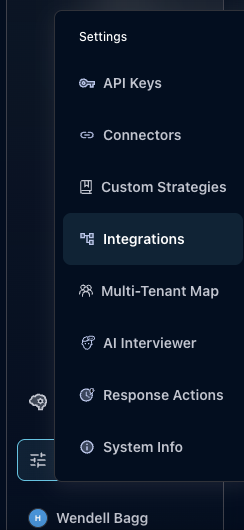
Integrations Dropdown

Click Available
The Microsoft Sentinel Tile

The Microsoft Sentinel Alert configuration (pt 1)

The Microsoft Sentinel Alert configuration (pt 2)

The Microsoft Sentinel Alert configuration (pt 3)

The Microsoft Sentinel Alert configuration (pt 4)

The Microsoft Sentinel Alert configuration (pt 5)

The Microsoft Sentinel Alert configuration (pt 6)

The Microsoft Sentinel Alert configuration (pt 7)